Difference Between Deep Web and Dark Web
A common misconception among those outside of the IT industry is that the terms “deep web” and “dark web” are interchangeable. These two realms are different, and it is important for you to know which is which to better protect your organization from cybercriminal activity.
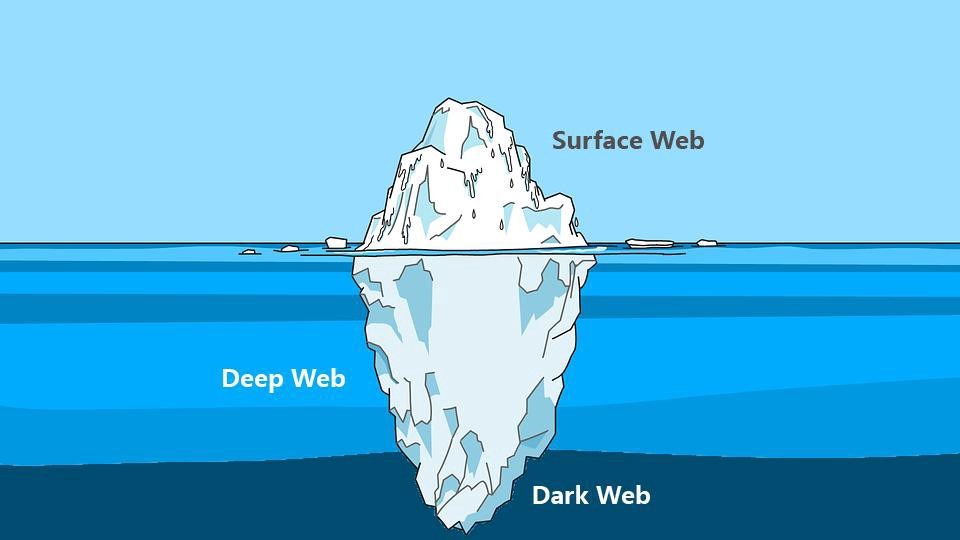
First off, the deep web is a vast platform and, yes, the dark web is part of it. So, they are not opposite and have some similarities. Simply put, the deep web is the part of the internet that can’t be accessed by search engine. The deep web holds material that requires a login to access, as well as pages with a paywall. Think of your bank account – you can search for your bank’s homepage without logging in, but you need your login and password to view details about your account.
The dark web is a small portion of the deep web, meaning it isn’t indexed by search engines, as well. Access to the dark web requires the installation of specialized software designed to handle the necessary encryption. While most of the websites on the dark web are used for illegal activities, not all websites are illegal on the dark web.
The Onion Router (TOR) is required to surf the dark web. It is one of the most widely used dark web overlay networks. Special software is required to access TOR sites, which have an “.onion” root. A TOR browser is required because it creates a random path of relays, each with its encryption, which helps to connect the sites.
Once again, not all activity on the dark web is illegal! However, you should explore this portion of the internet at your own risk. There are plenty of cybercrooks lurking ready with phishing attacks and other malicious activities with the hopes of gaining information for a larger score.
Instead, leave the dark web investigations to a cybersecurity expert like 2W Tech. We rely on Dark Web ID from ID Agent, the industry’s first commercial solution to detect your compromised credentials in real time on the dark web. Using a proprietary technology, Dark Web ID vigilantly searches the most secretive corners of the Internet to find compromised credentials associated with your company, contractors, and other personnel, and notifies you immediately when these critical assets are compromised, before they are used for identity theft, data breaches or other crimes. Call 2W Tech today to learn more.
Read More:
What is Next for Cloud Computing?
Power BI On-demand Loading Capabilities for Large Models