Stay Compliant and Protected with Zero Trust Security
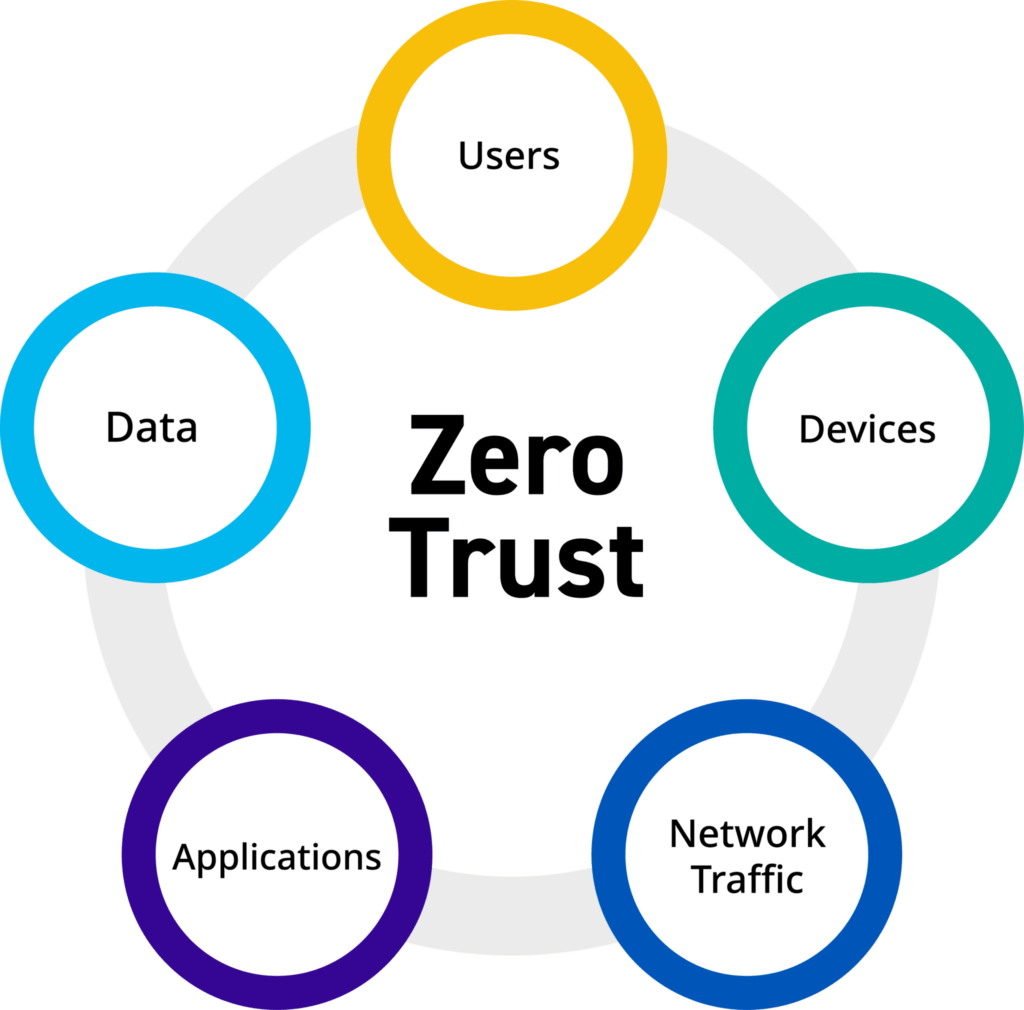
As remote and hybrid work models continue to be more prominent, organizations need a way to strengthen and secure growing boundaries. Add to that equation, the threat level to data security is more sophisticated than ever before. Zero Trust architecture is a critical component to modernizing security programs and ensuring sensitive data within an organization is stored safely. Not to mention, it can help stay compliant with regulatory standards.
Applying the Zero Trust principle of assume breach helps proactively minimize the impact of security attacks from internal and external bad actors. Security measures can be applied using all available data points and enforcing least privileged access to secure digital environments:
- Data classification and end-to-end encryption
- Sequence detection and user context to detect critical insider risks
- Policy configuration to prevent data loss
- Automated threat detection and response
Using redundant security mechanisms and system telemetry can help detect anomalies and help connect the dots to automation. This can help a business prevent, respond, and remediate data security incidents effectively.
One of the toughest issues with security is understanding if you are using the correct data security solutions and strategy. Zero Trust lens can help organizations implement the right protection to detect and remediate modern and evolving cyber risks and vulnerabilities in a timely, preventative measure.
Organizations must gain visibility into what assets exist within their organization. Then, assess their current risk and identify which assets should be prioritized and which one’s users are interacting with. Then several steps must be taken to secure sensitive data including:
- Gaining visibility
- Understanding insider risks
- Preventing data loss
- Leveraging dynamic controls
Microsoft’s Zero Trust security framework can also help your business meet regulatory and compliance standards by default. A Zero Trust model helps with understanding the policies needed to comply with governance requirements.
Where is your organization in your Zero Trust Security journey? This journey is a critical step your organization can take to modernize your security posture and exceed required regulatory and compliance standards. To learn more about implementing Zero Trust Security, call 2W Tech today. We are a Tier 1 Microsoft Cloud solutions provider and hold several Microsoft solutions designations. Let our team of expert IT Consultants guide you on your journey and help you ensure your organization is best protected from outside threats.
Read More:
Five Reasons to Attend Epicor Insights 2023
Artificial Intelligence to Drive Microsoft Revenue Growth