NIST Provides Mapping of IoT Device Cybersecurity and Nontechnical Supporting Capabilities
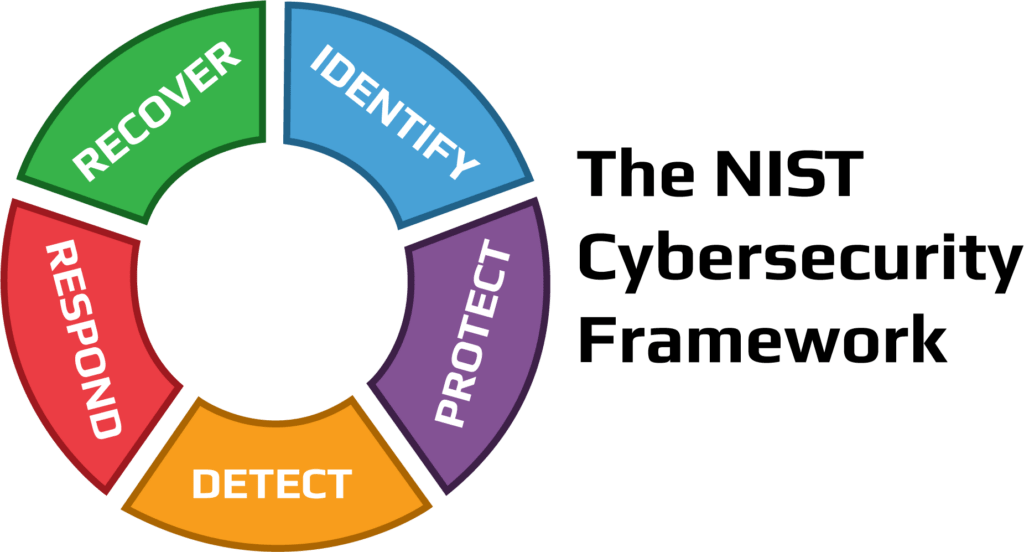
NIST is known for its intense Cybersecurity Framework, but it also has a reputation for providing collaboration between its programs. This includes the partnership between its National Cybersecurity Center of Excellence (NCCoE) and the Cybersecurity for the Internet of Things Program. Some recent project reports from the NCCoE include mappings of relevant IoT device cybersecurity capabilities and nontechnical supporting capabilities.
These three mappings align with NIST’s IoT cybersecurity guidance with real-world implementation approaches:
- Securing telehealth remote patient monitoring ecosystem
- Security distributed energy resources
- Protecting information and system integrity in industrial control system environments
The NCCoE is a collaborative hub where organizations across industries, government agencies and academic institutions work with NIST’s experts to address businesses’ most pressing cybersecurity challenges. NIST’s Cybersecurity for IoT Program supports the development of standards, guidance and related tools to improve the cybersecurity of connected devices and the environments in which they are deployed. To integrate IoT cybersecurity guidance into real-world scenarios, the IoT team has been working closely with the NCCoE. For this collaboration the IoT team identified NCCoE projects that incorporate IoT devices so this IoT-specific guidance can be leveraged by organizations looking to implement NCCoE’s modular cybersecurity solutions.
NIST’s Cybersecurity for IoT Program has defined a catalog of IoT cybersecurity capabilities. Device cybersecurity capabilities are cybersecurity features or functions that IoT devices provide through their own technical means. These capabilities include features like access control and data encryption.
Nontechnical supporting capabilities are actions that a manufacture or third-party organization performs in support of the cybersecurity of an IoT device. These include providing information about software updates, instructions for configuration settings and supply chain information.
Used together, these capabilities can help mitigate cybersecurity risks related to the use of IoT devices while assisting customers in achieving their goals.
For organizations implementing the NCCoE’s project’s example solution in their environment, the mapping demonstrates technical capabilities that organizations should look for in IoT devices. The mapping also lists nontechnical capabilities that they may look for from a manufacturer or third-party support in the IoT device. Selecting devices and manufacturers/third parties that provide these capabilities can facilitate the secure deployment of IoT devices into the organization’s environment.
If you need help reinforcing your cybersecurity stance through regulatory compliance and tightened controls, we can help. Contact 2W Tech today to get started with your Cybersecurity Compliance Program and let our IT consultants do the work for you.
Read More:
New Microsoft Teams Features May 2022
Why it is Time to Merge IT and OT